Did you setup your MFA forward?
As everyone know, Microsoft forced MFA for every user who want to access Azure portal. From my side I absolutely agree with this direction, I would say it is a must have for everyone. If you use only EntraID than dont have any problem, but if you have a federated environment and your ADFS or other IDP do the MFA, than you need to forward the MFA claim to EntraID. In my testlab I had to play with ADFS and EntraID and only for test purpose I faked the MFA claim. In this blogpost I will show you how to check if your MFA claim is forwarded or not and how I faked it.
Without MFA forward
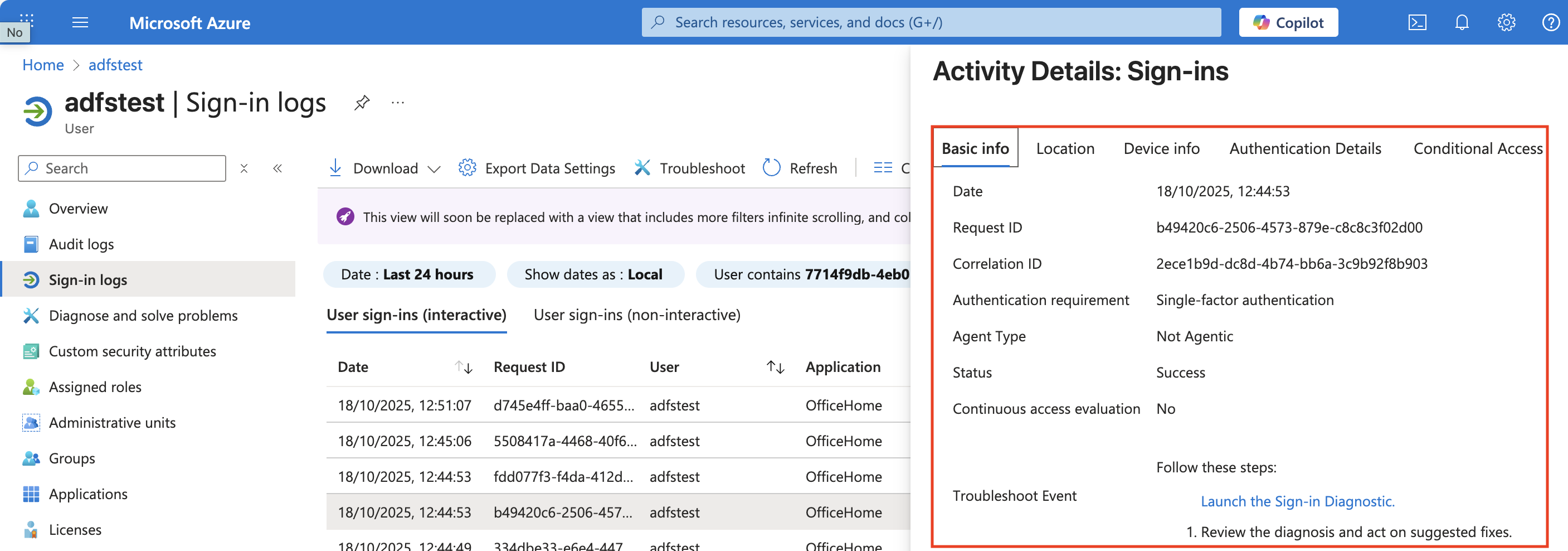
If you dont forward the MFA claim from your ADFS to EntraID, than you will see this in the sign-in logs:
Edit the ADFS claim rules
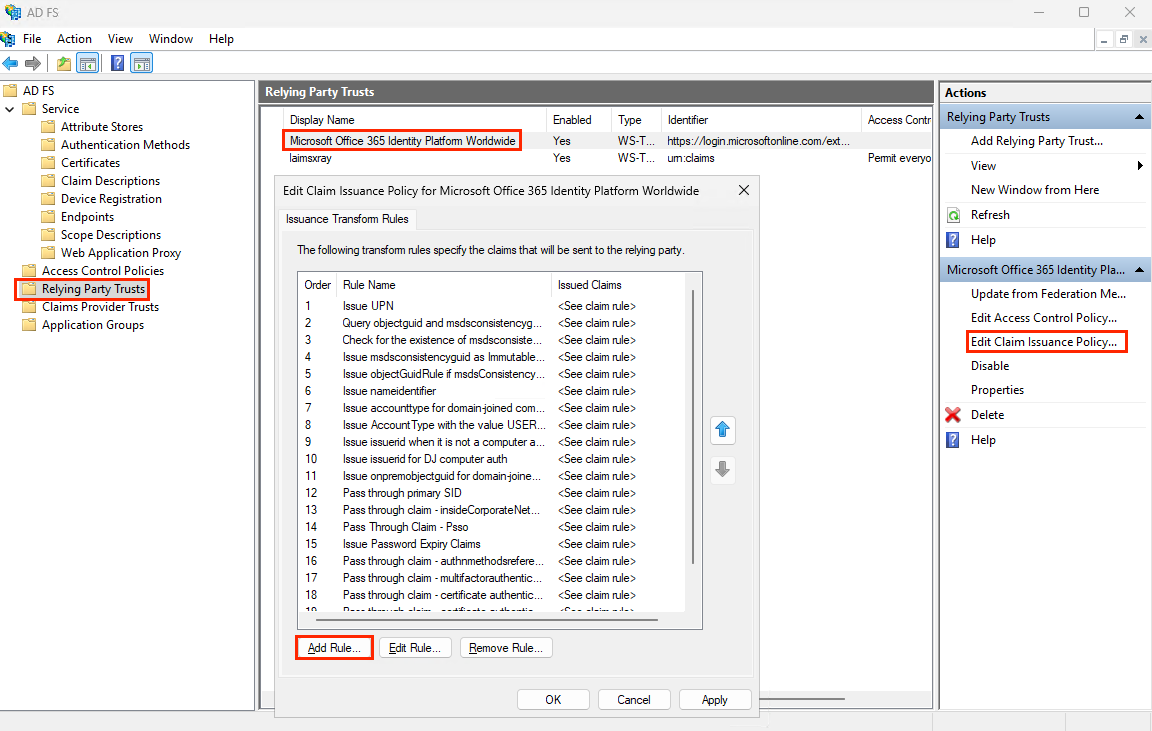
If we have the base ADFS settings, thsn we need to edit the Relying Party Trust and edit the Microsoft Office 365 Identity Platform Worldwide. In the Edit Claim Issuance Policy we need to add a new rule, which will forward the MFA claim.
Than Add Rule -> Send Claims Using a Custom Rule - Next
and add this rule:
1
=> issue(Type = "http://schemas.microsoft.com/ws/2008/06/identity/claims/authenticationmethod", Value = "http://schemas.microsoft.com/claims/multipleauthn");
And finish the wizard.
With MFA forward
After adding the claim rule, we can see the forwarded MFA claim in the sign-in logs: 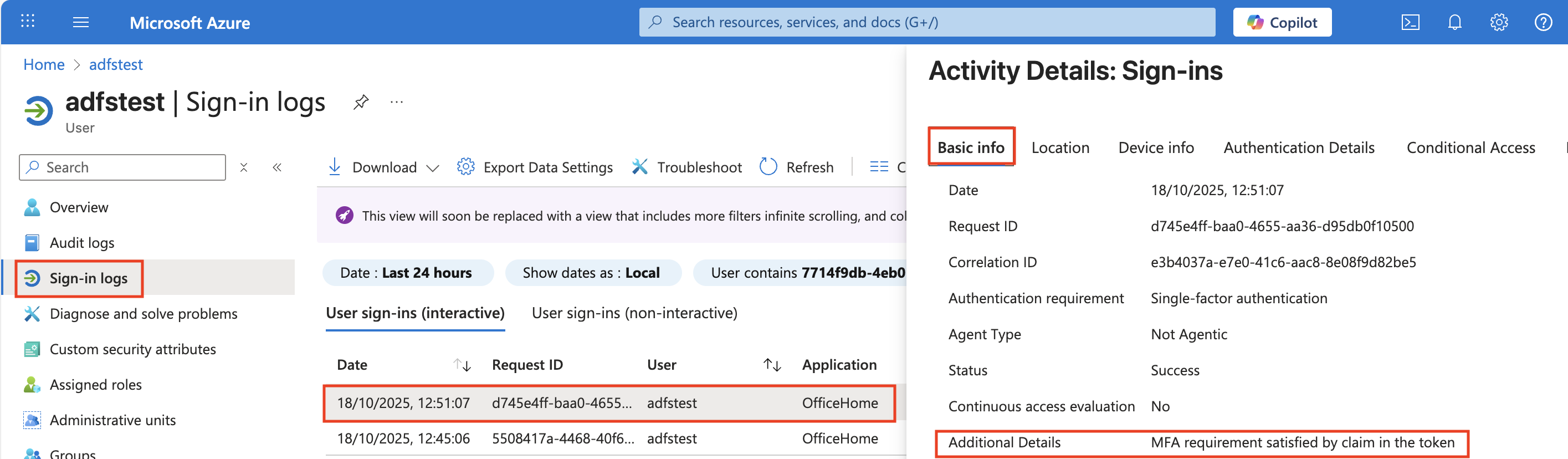
As you can see, the Authentication Details show that the user has authenticated using Multi-Factor Authentication (MFA). This indicates that the MFA claim has been successfully forwarded from ADFS to EntraID.
NEVER USE IN PROD (danger)
Never Use this solution in Production! This is only for test purpose! If you use Federation, than you have to forward the MFA claim from your IDP to EntraID!